Do you want to target software vulnerability and deny a user from accessing a network or website? This article is here to help. This article provides you with the best DDOS attack tools to help you restrict a user’s access to websites, emails, or networks.
A denial of service (DoS) attack is one in which the intended target is denied access to a service or resource. A DDoS assault, also known as a distributed denial of service attack, is carried out by a swarm of infected computers aimed at a single target. Data packets are sent in a torrent over the network.
DDoS attack tools are many, and they can be used to launch a variety of different types of attacks on a server. In case you have been in search of the best DDOS attack tools to use, here is a curated collection of popular Distributed Denial of Service (DDoS) Attack Tools. These listings have with their descriptions of what makes them effective. The lists here are free and paid DDoS tools.
1. DDoS Attack — The most effective method for spotting communications with command and control servers

- Free Option: 30 days free trial
- Platform: Linux and Windows
DDoS attacks are a great way to see whether your website is under assault. You can keep tabs on activity from any browser or server that has connected to your website thanks to this program’s features. You can securely monitor for and stop DDoS assaults in their tracks this way. SolarWinds provides this software with a wide range of capabilities. Using the program, DoS assaults can be spotted. The inquiry and response can be done instantly.
2. PRTG — Facilitates the generation of web pages in the format of your choice that include the most recent monitoring data

- Free Option: 30 days free trial
- Platform: Linux and Windows
As such, it is a tool rather than an active participant in the assaults themselves. However, its functionality can be valuable in reducing the impact of distributed denial-of-service assaults. The acronym PRTG stands for Paessler Router Traffic Grapher. For statistical purposes, such as measuring the volume of traffic on a server or the size of a network’s bandwidth utilization and alerting administrators to any unexpected changes, it is employed.
This monitoring software does exactly what its name suggests: it provides you with information on the health of various parts of your computer, network, or server. Almost every kind of operating system is supported, and it has a straightforward interface (OS). Volume-based denial of service assaults is where it shines.
3. Low Orbit ION Canno (LOIC) — Allows you to launch a distributed denial-of-service (DDoS) assault on any of their managed websites

- Free Option: Free Download
- Platform: Windows
This weapon’s full name is the Low Orbit Ion Cannon. It’s particularly effective in distributed denial of service (DDOS) assaults that rely on massive amounts of data. In layman’s terms, it directs computers’ network traffic toward designated server architectures. Because no one computer can generate enough demand to overrun server bandwidth, these attacks cause networks to transmit packets to servers that were not specifically requested.
4. GoldenEye — A simple Python script that can be used as a DDoS utility

- Free Option: Free Download
- Platform: Windows
Similar to the last tool, this one is meant for use in simulations. It can be used to simulate a variety of distributed denial of service attacks on the servers. After identifying potential vulnerabilities, the tester watches the security system’s reaction to determine the best course of action.
Servers are the intended target audience for this utility. Despite being intended as a testing tool for servers, hackers have found a way to use it to launch massive distributed denial of service (DDOS) assaults.
5. DAVOSET — Gives you the option of launching an assault straight from the command line

- Free Option: Free Download
Attacks on other websites can be carried out with the use of this tool. The use of this technique in cyberattacks has been more well-known in recent years. Manipulated structures are often utilized in the communication between websites. It takes advantage of vulnerabilities in several data architectures, including XML external entities.
6. Tor’s Hammer — Enables you to use Markdown for formatting text content

- Free Option: Free Download
- Platform: Windows
The program can conduct assaults inside the Tor network, as the name indicates. Tor’s Hammer attacks all layers of the TCP stack by default, which is level 7 of the OSI model. Its operation is straightforward. As a consequence of the tool opening several dead connections, the program becomes stuck and cannot produce results. While it can seem like Thor’s Hammer, this weapon is designed for stealthy strikes rather than shattering blows.
The program was developed to circumvent security measures like firewalls by exploiting users’ need for anonymity. In addition, penetration testers use it to simulate assaults on security systems. The main network (Tor) is often quite sluggish, which is a major drawback of this technology. The effectiveness of such devices is limited by speed restrictions.
7. RUDY — Best DDOS Attack tool with a Simple Interface

- Free Option: Free Download
- Platform: Windows
RUDY is an acronym for “R U Dead Yet?” To launch a coordinated and gradual denial-of-service assault on servers, it makes use of lengthy forms. RUDY is often used with other devices. The first step is to find a server hosting the necessary online forms. After these servers and forms are identified, the RUDY attack tool is used to make very lengthy hypertext transfer protocol queries.
8. OWASP HTTP POST — Supports testing against threats at the app layer

- Price: FREE
You can check how well your apps perform using OWASP HTTP Post. Specifically, it conducts evaluations of network performance. I can’t think of a better approach to launch a free Distributed Denial of Service attack on your server. This program facilitates the dissemination of your software utilities to others. This means more than just one of your team’s cybersecurity experts has access to the tools at their disposal.
As a result, communication is enhanced. In addition, it makes sure that everyone is aware of your software’s security status. Even though there is no payment associated with using this tool, you can use it for business purposes without any concerns.
9. PyLoris — Best DDOS Attack Tool with a Simple Graphic User Interface
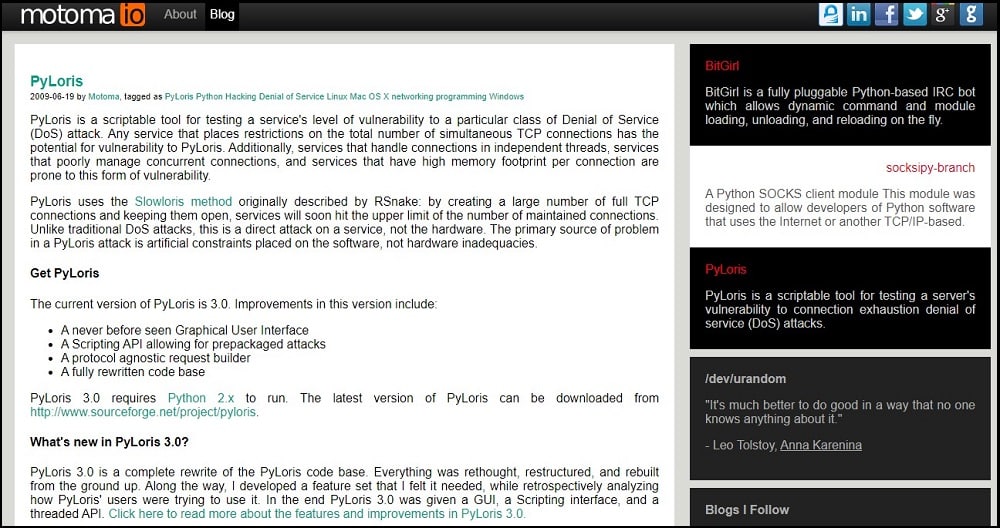
- Free Option: Free Download
- Platform: Linux, Windows, Mac OS
This class of tools is excellent for conducting covert Distributed Denial of Service assaults. It’s another instrument for conducting covert and methodical assaults during penetration testing. It’s used in direct service denial of service attacks.
To maintain privacy and security, it makes use of encrypted server-to-server communication mechanisms. SSL proxies and SOCK proxies are two of the most common types. Common server protocols like HTTP, UDP, and so on are used over these channels.
10. DDoSIM — Best for establishing complete TCP connections to the specified server

- Free Option: Free Download
- Platform: Windows
The primary use of this program is to simulate denial-of-service (DDOS) assaults on specific servers at the application layer. This program simulates many hosts, each of which can then be used to launch layer 7 attacks against the targeted servers. The effectiveness of the server’s security system is tested by its reaction to this kind of assault.
The program is developed in C++, and although it can be used with other OSes, it performs best on LINUX. This program is designed to demonstrate the breadth and depth of a hacker’s mind by using a variety of attack techniques.
11. HULK — Best for Bypassing Server Cache Server

- Free Option: Free Download
- Platform: Windows
Something like “HTTP Unbearable Load King” can be an abbreviation for this. These days, computers often connect with servers using transfer protocols, making it easy for assaults to overwhelm them with a large number of seemingly genuine requests. This is precisely what HULK does.
Due to its capacity to deliver disguised traffic, HULK is surprisingly effective at performing denial-of-service attacks. At last, these resources can be leveraged to develop assaults that are hard to spot. Naturally, it is to be anticipated, given that HTTP is used as the execution medium.
12. Sucuri — Keeps tabs on all the security-related patch updates and server rules

- Price: begins at 199.99 USD yearly with 30 days guarantee
To defend yourself against Distributed Denial of Service (DDoS) assaults, you can download Sucuri, a free program. There’s sophisticated gear like an Intrusion Prevention System (IPS) and a Web Application Firewall at work here (WAF). This program offers full defense against viruses and hacks. Your website will be protected from harmful code and material thanks to the Web Application Firewall (WAF).
Your network is safe from intruders thanks to the WAF, which blocks their harmful attempts at entering it. In addition, Sucuri prevents Zero-Day attacks. Simply put, a Zero-Day exploit is a flaw in a piece of software that has gone undiscovered by or is beyond the control of the creator of the product.
13. High Orbit ION cannon (HOIC) — Allows you to select the number of threads in the present attack

- Free Option: Free Download
- Platform: Mac OS, Linux
It’s possible to attack many URLs at once using HOIC, a free, open-source DDoS tool. It’s a program for initiating DoS attacks using HTTP POSTs. The maximum number of simultaneous DDoS attacks that can be launched with this tool is 256. It’s a fantastic method for gauging your website’s resilience against malicious intrusion. Furthermore, you can use this instrument to gradually learn how much storage space your server provides.
To help with this, HOIC provides a counter displaying the total number of assaults on the website. This will allow you to choose the threshold above which your server will go down. You can also adjust the current DDoS attack’s thread count to suit your needs.
This gives you more say over the kind of things you put through your tests. The greatest aspect is that this DDoS tool is easily portable to Mac OS X and Linux. You can adjust the parameters to make the assault less or more powerful.
FAQ
Q. How do DDOS attack tools function?
Tools used in DDoS attacks identify weak points in a server or network and exploit them by planting malware. When a network has enough compromised devices, DDoS attack tools tell them all to launch a coordinated assault on the server, flooding it with requests and causing it to crash from overload.
Q. Is it simple to launch a denial-of-service attack?
Millions of websites across the globe are hit by DDoS assaults each year, and that figure is only expected to grow.
Q. Is it expensive to use a DDOS attack?
The price tag of a distributed denial of service (DDoS) attack on your IT Company or a client’s business can rapidly balloon due to lost income and data. The typical cost per assault for a small to medium-sized firm is 120,000 USD.
Q. Can I use a Virtual Private Network (VPN) to protect myself against a Distributed Denial of Service (DDOS) attack?
Yes, VPNs can prevent Distributed Denial of Service assaults in general. Primarily, a VPN is useful because it conceals users’ real IP addresses. Hide your IP address to make it more difficult for distributed denial of service (DDoS) attacks to target your network.
Conclusion
And there you have it! In this day and age, you must take measures to keep your website safe against distributed denial of service assaults.
However, if you aren’t ready for a DoS assault, your web server might be in danger. Your server will immediately fail if you don’t implement even the most basic security measures.
How can you test your web server’s resilience against Denial of Service and Distributed Denial of Service attacks?
Thankfully, there are resources on the web that can help you practice for such assaults. Some tools function by defending users from harm. And they permit you to dig further.